第三期
发布时间: 2022-08-28
文章
How SHA-256 Works Step-By-Step
SHA-2(安全哈希算法2)是SHA-256的一部分,是最流行的哈希算法之一。在本文中,我们将进一步分解SHA 256加密算法的每个步骤,并手动完成一个真实示例。
Like we mentioned above, a cryptographic hash function generates a “fingerprint” for a given input string. For example, if we were to hash the entire text of JRR Tolkien’s “The Lord of The Rings” series using the SHA 256 algorithm, we would get a 256-bit output almost unique to that book’s text. If we changed even a single letter in the book, the output hash would be wildly different.
It’s worth noting that we say the output of a hash is “almost unique” because there are a finite number of output strings. After all, the output of SHA-256 is always 256 bits long, which means it has a fixed size. The number of possible inputs, however, is infinite, meaning some inputs will hash to the same output. When this happens, it’s called a “collision”, and it is nearly impossible.
网道
网道(WangDoc.com)是一个文档网站,提供互联网开发文档,正在建设中。
这个项目的目标是,提供高质量的、拥有自主版权的、可以自由使用的中文软件文档。
网站的所有内容采用知识共享 3.0 许可证,与维基百科相同。
你可以自由使用本站所有内容(包括用于商业用途),不必支付任何费用,条件是使用时保持署名(“来自网道项目”),以及采用相同方式共享。
所有文档仓库都托管在 GitHub,你可以在那里追踪项目进展。
为网站添加用户友好的深色模式支持
文章教你如何为你的网站加上支持 手动调节和自动跟随系统模式 的黑暗模式。
「深色模式」更像是一个主题,即使在白天也可以使用。不论是为了在 OLED 屏幕上省电、亦或是减少白光刺激护眼、亦或是暗色模式对色盲用户更加友好,总之 macOS 率先提出了系统级的「暗色模式」、并在 WebKit 中增加了对应的 Media Query,而后 Chromium、Firefox 先后跟进,如今兼容 prefers-color-scheme 的浏览器占有率已经高达 81.82%。
Making setInterval Declarative with React Hooks
使用React Hook 的时候,会发现setInterval 和 hooks 并不能很好的配合使用;本篇文章提出了几种解决方案。
I think Hooks provide lower-level primitives than classes — but their beauty is that they enable us to compose and create better declarative abstractions.
工具
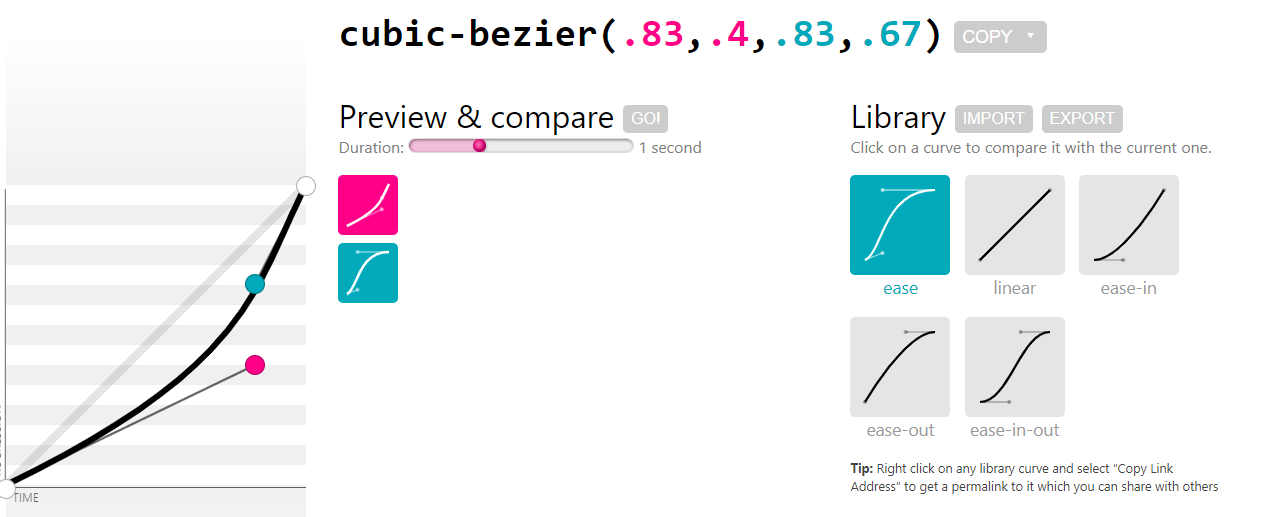
cubic-bezier()
一款让 cubic-bezier() 更简单的工具
neumorphism
新拟态设计网站,可以自己调节并生成代码。
uiverse.io
一款好看的、优秀的web设计网站,可以提供源代码,也许可能会给您提供设计心得。